How North Korea Converts Stolen Crypto to Cash: The Laundering Blueprint

Converting stolen digital assets into stolen cryptocurrency fiat is a high-stakes game of hide-and-seek. North Korea doesn't just 'sell' its loot; it runs a sophisticated industrial-scale laundering operation. They've moved past simple tricks, now utilizing a global network of shell companies, fake identities, and regulatory loopholes to bypass sanctions. For them, the blockchain isn't just a ledger-it's a gold mine that requires a very specific set of tools to refine.
The Four-Step Pipeline from Theft to Cash
North Korea doesn't move funds in a straight line. To avoid being caught by blockchain analysts, they use a multi-stage process that breaks the digital trail. Think of it like a series of car washes; by the time the money reaches the end, the original 'dirt' is gone.
- The Heist: It usually starts with a phishing attack or a system compromise. According to FBI data, this accounts for 68% of their attacks. They steal the assets from exchanges or bridge protocols.
- The Shuffle: Once the funds are out, they use Cross-chain bridges tools that allow users to transfer assets from one blockchain to another. In 2024, bridges like Ren Bridge and Avalanche Bridge processed over $1.2 billion in linked transactions. This makes it incredibly hard for investigators to follow the money as it hops from Ethereum to Solana or Binance Smart Chain.
- The Pivot to Bitcoin: Most stolen assets eventually land in Bitcoin the first and most liquid decentralized digital currency. Why? Because it has the deepest liquidity and the most widespread acceptance at OTC desks. About 82% of their final conversion targets are in BTC.
- The Final Cash-Out: This is where the digital becomes physical. They use third-party networks and exchanges with lax identity checks to swap the Bitcoin for fiat currency like US Dollars or Chinese Yuan.
The 'Flood the Zone' Tactic
If you try to move $600 million in one go, every alarm bell in the financial world goes off. Instead, North Korean hackers use a technique called 'flood the zone.' Rather than a few large transfers, they execute 400 to 500 high-frequency transactions every single day. By splitting the loot into thousands of tiny pieces across different platforms, they overwhelm the people trying to track them. During the Ronin Bridge hack, this method helped them obscure $625 million by making the volume of data too noisy for analysts to process in real-time.

The Secret Weapon: Overseas IT Workers
Software and scripts can only do so much. To truly bridge the gap between a digital wallet and a bank account, you need humans on the inside. North Korea deploys thousands of IT workers across China, Russia, and Southeast Asia. These aren't typical freelancers; they are state agents using fake identities-often pretending to be from India or Vietnam-to get hired by crypto exchanges and fintech firms.
Once they are inside a company, they create backdoors. This allows them to move funds with minimal oversight. In 2024, reports showed these workers helped bypass the standard 72-hour fraud detection windows, enabling direct wallet-to-bank transfers in as little as 12 hours. These workers essentially act as human 'cash-out' points, using their legitimate salaries and company access to bleach stolen funds.
The Geography of Laundering: Cambodia and China
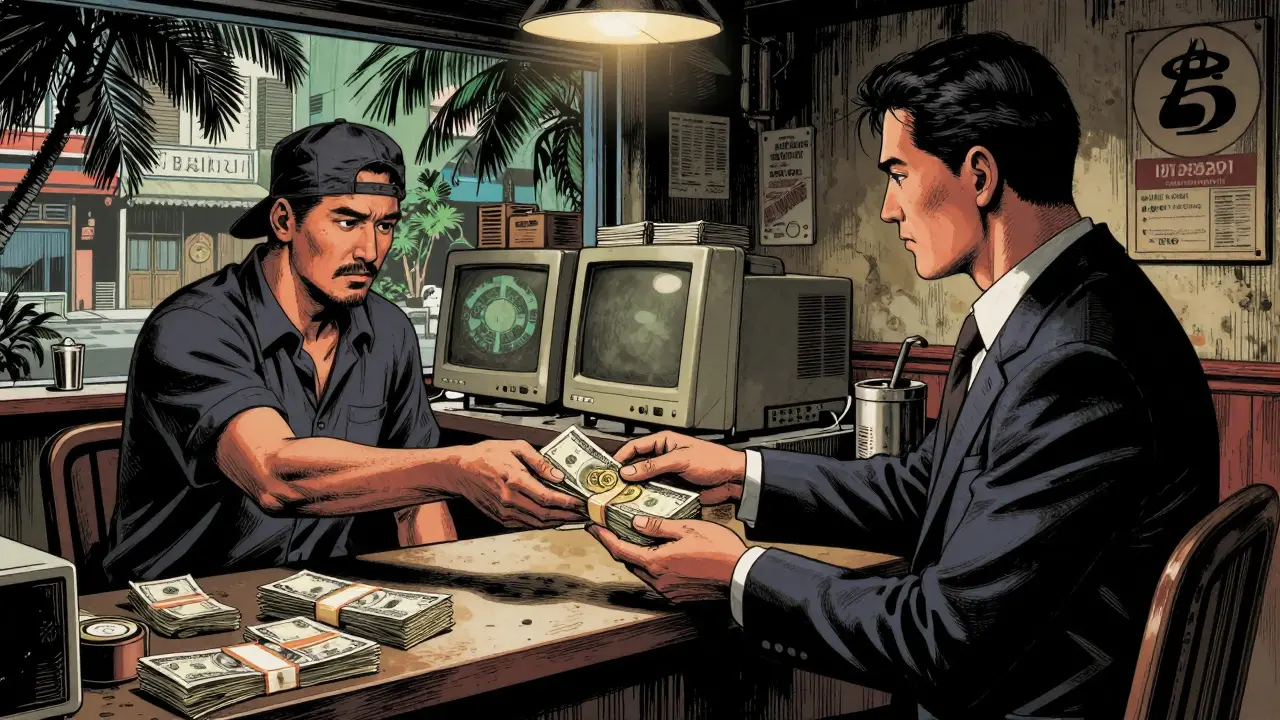
Where does the money actually land? While China remains a hub, Cambodia a Southeast Asian country with a loosely regulated financial sector that has become a primary hub for crypto laundering has emerged as the primary center. The lack of strict oversight makes it a playground for the regime.
A major player here is the Huione Group a Cambodian financial entity designated as a primary money laundering concern by FinCEN. They provide the infrastructure needed to turn illicit crypto into clean value. Some of their subsidiaries even issue non-freezable stablecoins, making it nearly impossible for international authorities to claw back the funds. In some regions, like Sihanoukville, the regime has even set up 'crypto cafes'-physical shops where you can trade crypto for cash with zero ID required. It's essentially a decentralized bank for stolen loot.
| Method | Speed | Risk Level | Primary Goal |
|---|---|---|---|
| Cross-Chain Bridges | Fast | Medium | Obscure origin |
| Overseas IT Workers | Slow | Low | Direct bank access |
| Gambling Platforms | Moderate | Low | Integration into legal funds |
| Crypto Cafes (Cambodia) | Instant | Very Low | Physical cash (Fiat) |
The Evolution of the Game
The rules are changing. For years, the regime relied on Tornado Cash a decentralized mixing service that obscures the trail of cryptocurrency transactions. But after the US sanctioned it in 2022, that door closed. Now, they've pivoted to Decentralized Finance (DeFi) and 'stablecoin arbitrage.' By swapping stolen assets for stablecoins like USDC through decentralized exchanges and exploiting price gaps between regional markets, they can generate 'clean' profits that look like legitimate trading gains.
Despite these shifts, the net is tightening. The implementation of the Crypto-Asset Reporting Framework is forcing exchanges to share beneficiary data across 100 different countries. This means there are fewer and fewer places to hide. While they are still successful, the window for easy cash-outs is closing. The regime is now recruiting blockchain developers from failed projects to build their own private protocols, hoping to stay one step ahead of the law.
Why does North Korea prefer Bitcoin for the final step?
Bitcoin is the most liquid cryptocurrency in the world. Because so many over-the-counter (OTC) desks and unregulated exchanges accept it, it is the easiest asset to swap for physical cash without triggering the red flags that more obscure tokens might cause.
What are 'crypto cafes' and how do they work?
Crypto cafes are physical storefronts, primarily located in regions like Sihanoukville, Cambodia. They operate as unofficial exchanges where users can trade cryptocurrency for cash (fiat) without providing any identification (KYC), effectively bypassing the global banking system.
How do IT workers help in laundering?
These workers gain employment at legitimate crypto firms using fake identities. Once inside, they use their access to move funds through the company's internal systems or create backdoors that allow the regime to bypass fraud detection and move money directly into bank accounts.
Can't blockchain analysis stop this?
Blockchain analysis can track the movement of funds, but it cannot stop the transaction itself. While tracking has improved by 40%, the regime adapts faster-using cross-chain bridges and 'flood the zone' tactics to make the trail too complex to follow in real-time.
What happened to Tornado Cash?
Tornado Cash was a 'mixer' that hid the origin of funds. After the US Treasury sanctioned it in September 2022, it became a legal risk for many to use, forcing North Korean groups to move toward cross-chain bridges and DeFi arbitrage to hide their tracks.